After traveling the world for the past 10-years, I’ve learned a lot about staying safe – sometimes the hard way. Here are my best travel safety tips for avoiding trouble on your trip.

Nothing ruins an adventure quicker than getting sick, scammed or robbed when you travel!
One time in Panama, some women distracted me at a bar while stealing my laptop from a backpack.
In Mexico, a pickpocket grabbed my iPhone on the street. I managed to get that back too, chasing the thief down the road screaming like a maniac and brandishing a bottle of tequila! LOL.
You don’t even need to travel internationally to have bad stuff happen. In Miami Beach, my camera was stolen when I wasn’t paying attention.
After many years traveling the world, I’ve grown accustomed to deceitful taxi drivers, two-faced tour guides, insincere offers of help, and an occasional theft or scam.
For the most part, the world is a pretty safe place for travelers. I don’t want to scare you too much! However, it’s wise to be prepared.
With that in mind, here are my best travel safety tips to help minimize your chances of something bad happening to you during your travels.
Jump to:
- Top Travel Safety Tips
- 1. Learn Common Travel Scams
- 2. Write Down Emergency Info
- 3. Check The State Department Website
- 4: Lock Up Your Valuables
- 5: Get Travel Insurance
- 6: Ask Locals For Advice
- 7: Register With Your Embassy
- 8: Email Your Itinerary To Friends/Family
- 9: Don’t Share Too Much With Strangers
- 10: Don’t Do Stupid Things For Photos
- 11: Splurge On Extra Safety
- 12: Be Aware Of Your Clothing
- 13: Stay “Tethered” To Your Bag
- 14: Learn Basic Self-Defense
- 15: Project Situational Awareness
- 16: Tell Your Bank Where You’re Going
- 17: Hide Emergency Cash
- 18: Food & Water Safety
- 19: Use ATMs Wisely
- 20: Stop Using Your Back Pocket
- 21: Travel In Numbers
- 22: Pack A First Aid Kit
- 23: Stay (Relatively) Sober
- 24: Trust Your Instincts!
- 25: Travel Safety For Women vs. Men
- A Few Words About Risk…
Top Travel Safety Tips
1. Learn Common Travel Scams

Wherever you go in the world, you’ll always find people ready to trick you out of your hard-earned cash. If you’re lucky, they’ll be kinda obvious – but there are plenty of craftier, professional con-artists out there too.
Everyone thinks they’re too smart to be scammed — but it happens.
Here are some of the most common travel scams I’ve come across. I recommend you learn them all – then fire up the Google and do even more in-depth research into the worst scams happening at your specific destination.
For example, the milk scam in Cuba. “Broken” taxi meters in Costa Rica. Or the famous ring scam in Paris. Every country has its own special scams to watch out for!
Forewarned is forearmed, and this research can help defend you from being tricked out of hundreds, maybe thousands of dollars (while suffering the kind of frustration and misery that ruins a dream trip).
2. Write Down Emergency Info
If disaster strikes, you might not have time to search for numbers for local police or ambulance services, or directions to the nearest embassy for your country. You may also be too stressed and panicky to think straight.
Don’t put yourself in that position. Instead, record that information in advance, and create an “Emergency Plan” for you to follow if things go badly. Save it on your phones Notes app.
Save all your important documents to the cloud, so you can access them while traveling abroad. Things like a copy of your passport, birth certificate, travel shots, drivers license, and anything else you might need.
That way, if something goes wrong while traveling, you’ll always have access to your documents, plus know exactly who to call and where to go for help.
3. Check The State Department Website
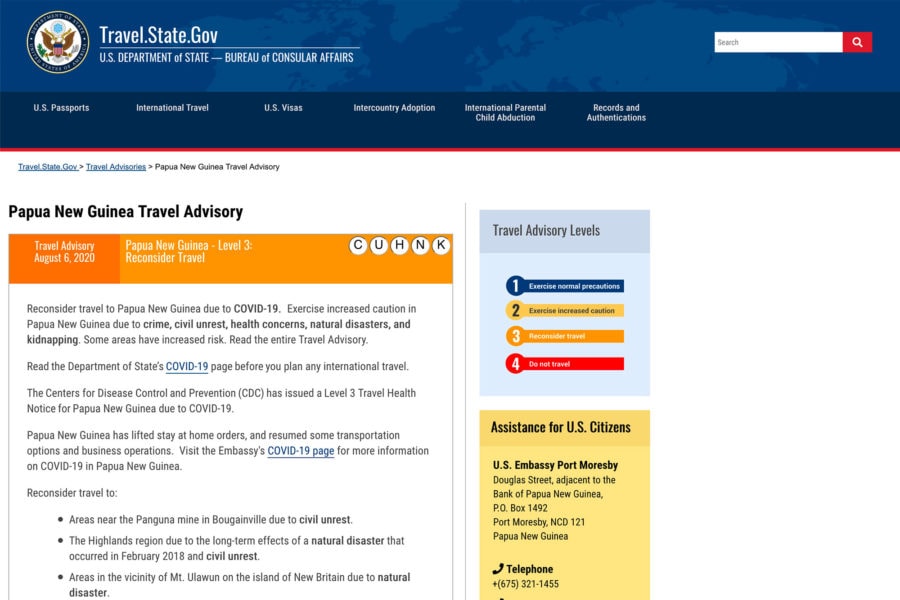
The U.S. Department of State has a travel advisory page for every country in the world, where it lists all known difficulties and current threats to the safety of visitors.
However, a big caveat for this one: it’s the State Department’s job to warn you about everything that could go wrong, which is sometimes different to what is likely to go wrong.
This means their advice is generally on the hyper-cautious side. Factor that in, while you dig up more on-the-ground information.
But researching travel warnings will give you a general idea of what’s going on in the country you’re visiting, and specific problem areas you may want to avoid.
For example, just because certain parts of Thailand or Mexico have problems, doesn’t mean you should completely avoid those countries altogether.
4: Lock Up Your Valuables

Putting aside the fact that traveling with anything super valuable is usually a bad idea, there will always be something you absolutely cannot afford to have stolen. I travel with a lot of expensive camera gear for example.
Your job is to minimize the easy opportunities for theft.
Firstly, know that most travel backpacks aren’t very secure. It’s easy to feel that a zipped, even locked bag is a sufficient deterrent to any thief, and doze off next to it. Waking up to find someone’s slashed a hole in the side!
Unless it’s a slash-proof backpack, the material can be cut or torn by anyone determined enough. Many zippers can be forced open with sharp objects like a writing pen.
Always be aware of your valuables, and try to keep an eye on them in such a way that it would be impossible for someone to steal without you knowing. I’ll use my backpack as a pillow on train/bus routes that have a reputation for theft, and will sometimes lock it to a seat using a thin cable like this.
Secondly, call your accommodation to ask about secure storage options like a room safe, lockers, or a locked storage area. Carry your own locker padlock when staying at backpacking hostels.
5: Get Travel Insurance
You never think you need it, until you do. If you’re really worried about the safety of yourself and your gear while you travel, you can almost completely relax if you have some good insurance.
People ask me all the time if I’m worried about traveling with an expensive computer and camera. I was, when I didn’t have insurance for them. Now that I do, I’m not worried. If stuff gets stolen, it will get replaced.
Everyone should carry some kind of health and property insurance when traveling. Why? Because stuff happens. Whether you think it will or not. It doesn’t matter how careful you think you are.
My recommendation is SafetyWing for short-term travel insurance. They make it super easy to buy online.
If you’re going to be traveling for a long time (like as a digital nomad), there are good long-term options like expat health insurance from SafetyWing Remote Health mixed with photography/computer insurance from TCP Photography Insurance.

Get Travel Insurance
Protect yourself from injury, illness, or theft while abroad. SafetyWing offers affordable travel insurance.
6: Ask Locals For Advice
If you really want to know which neighborhoods are safe and which might be sketchy, ask a local resident of the area.
Most locals are friendly, and will warn you about straying into dangerous areas. On the other hand, if a stranger offers up advice, it’s also wise to get a second opinion – just in case they don’t really know what they’re talking about but simply wanted to help (or worse, are trying to scam you).
Taxi drivers can be hit or miss in this regard. Some can be excellent sources for good information, others are miserable assholes who might actually lead you into trouble.
I’ve found that hostel or hotel front desk workers are generally pretty good sources for local advice.
Don’t be afraid to ask them which parts of the city to avoid, how much taxi fares should cost, and where to find a great place to eat!
7: Register With Your Embassy
The Smart Traveler Enrollment Program, from the U.S. Department of State, is designed to make a destination’s local embassy aware of your arrival and keep you constantly updated with the latest safety information.
It’s free, it’s available for all U.S. citizens and nationals living abroad, and it’s a great way to get reliable, up to date safety information as you travel, along with an extra level of security in case of emergencies.
Canada has it’s own version, called Registration Of Canadians Abroad.
That way if an emergency happens, like a natural disaster or terrorist attack, the local embassy can get a hold of you quickly to share important information or help with evacuation.
8: Email Your Itinerary To Friends/Family

Once you’ve worked out where you’re going and when, make sure someone else knows too.
The best way is to email the full itinerary to a few family members (and double-check with them that they received it – don’t just assume it landed in their Inbox, make sure it did). Then, if you can, check in from time to time.
Before I travel anywhere, I make sure my parents know where I’m going, what my general plans are, and when I should be back.
That way, if they don’t hear from me for a few days after I’m supposed to return, they can help notify the proper local authorities, the embassy, etc.
9: Don’t Share Too Much With Strangers
If you’re ever tempted to make your itinerary more public, say in a Facebook post, just remember it can be a roadmap of your movements – just the sort of thing someone with ill-intentions would love to know.
I also don’t recommend sharing too many details about your travel plans or accommodation details with people you’ve just met. For example, don’t tell a local shop owner or street tout where you’re staying when asked.
If someone does ask, rather than be rude, you can be vague about an area of town rather than the name of your hotel. Or lie and name a hotel you’re not actually staying at.
Sometimes people will ask if it’s your first time visiting their country or city. If you don’t trust them yet, you can pretend it isn’t your first trip. Because sharing that you’re new might also signal you’re a good target for scams.
When feeling vulnerable in a strange place, little white lies won’t hurt.
10: Don’t Do Stupid Things For Photos

In the age of Instagram & TikTok, it often feels like tourists are engaging in increasingly riskier activities just for likes on social media. Every week now you hear about people falling off cliffs or getting attacked by wildlife because they were trying to get an awesome photo.
Know your personal limits! Don’t do stupid things that have a high potential to get you hurt or killed. I’ll admit I enjoy a bit of risk now and then, but I try to be smart about it.
Don’t stand on the edge of a cliff if it’s windy or looks unstable. Pay attention to posted signs and warnings wherever you go. Keep your distance from wildlife, because animals are unpredictable.
Put yourself in the shoes of the locals, be respectful of the places you visit, and don’t trespass on private property either.
READ MORE: Is Instagram Ruining Travel?
11: Splurge On Extra Safety
If you’re traveling as a budget backpacker, like I was, it can be tempting to save as much money as possible with the cheapest accommodation, the cheapest flights, the cheapest activities.
But it’s important to know that this isn’t always the safest way to travel.
Ultra cheap backpacker hostels aren’t always the safest places. I’ve stayed in some without locks on the doors, that felt like make-shift homeless shelters for drug addicts and other seedy people.
Budget flights can often arrive in the middle of the night — usually not the best time to be hailing down a cab in a dangerous city and hoping the driver doesn’t abduct you.
Sometimes it’s worth the extra few bucks to splurge on a slightly better hostel, a more convenient flight, a taxi home from the bar, or a tour operator with a strong safety record.
12: Be Aware Of Your Clothing

When it comes to travel, the wrong clothes scream “TOURIST” and make you a target for scammers, thieves and worse. The less obviously a visitor you look, the less attention you’ll get from the wrong kind of people.
Wearing the right clothes is a sign of respect. Many Islamic countries have specific dress code guidelines that are often strictly enforced – and other destinations have laws that may catch you out (for example, walking topless through the streets of Barcelona is illegal for both sexes).
However, it’s possible to stay within the law and still offend locals with what you’re wearing – generating a lot of hostility towards you in the process. Ignoring local customs can come across as both arrogant and ignorant.
In conservative countries, it’s just safer to dress more conservatively yourself. Obviously as a foreigner you’re still going to stand out a bit, but much less than those who ignore the local customs.
Start by checking out Wikipedia’s general advice on clothing laws by country – and then narrow down your research until you find someone giving advice you can trust, ideally a resident or expat turned local.
13: Stay “Tethered” To Your Bag
Most quick snatch-and-run type robberies happen because the thief can do it easily, and has time to get away. Therefore, anything that slows them down will help prevent it in the first place.
If you can keep your bag tethered to something immovable at all times, and do so in a really obvious way, thieves will consider it way too risky a job – and leave you alone.
A simple and effective method is to use a carabiner clip. Even a regular strap around your leg or chair.
It doesn’t need to be secured with a steel cable and padlock all the time, just attached to something that will make a snatch-and-run attempt too difficult.
14: Learn Basic Self-Defense

You don’t need black-belt skills, but joining a few self defense classes is a worthwhile investment in your personal safety. Some good street-effective styles to consider are Krav Maga or Muay Thai.
Next, learn WHEN to apply it. Just because you can kick someone’s ass, doesn’t mean you should in all situations. In the words of author Sam Harris:
“Do whatever you can to avoid a physical confrontation, but the moment avoidance fails, attack explosively for the purposes of escape.”
A great way to neutralize a threat is to get yourself as far away as physically possible. If someone with a gun or knife just wants your phone, give it to them, run away, and live another day.
Use force only when your life is threatened & there are absolutely no other options available.
15: Project Situational Awareness
Did you know that a majority of human communication is based on non-verbal body language? This projection of confidence can prevent you from becoming a target.
Keep your head up, stay alert, and aware of you’re surroundings. When you’re confident, potential attackers can sense it through your body language and eye contact.
Most will choose to move on and find an easier victim to attack.
In many places, making direct eye contact with potential threats can help ward off an attack, ensuring they notice you see them and what they may be planning. Yet in other parts of the world, too much eye contact might invite trouble…
Generally you should stay aware of who is around you, walk with a purpose, and don’t look worried, lost, or scared (even if you feel that way) — but I’d also avoid staring contests with sketchy looking strangers.
16: Tell Your Bank Where You’re Going

Imagine the agony of doing absolutely everything right and keeping yourself perfectly safe and secure – only to have your trip ruined because your bank thinks you’re the thief, and locks down all your cards.
If this happens and you’re lucky, you’ll be asked security questions to determine your identity. The rest of the time, you’ll get a notification from the bank’s fraud detection team that irregular activity has been recorded on your card, and they’ve put a hold on all transactions until the situation is resolved – which might take days.
The solution is simple. Most online banking services have a facility for letting the bank or credit card provider know about your upcoming travels. Make sure you use it, shortly before leaving – and keep them in the loop if your travel plans change.
I also recommend using your debit card at the airport ATM machine as soon as you arrive in a new country, as this also helps let the bank know you’re traveling.
READ MORE: Travel Banking Tips & Advice
17: Hide Emergency Cash
While it’s good to do everything you can to prevent worst case scenarios – it’s equally smart to assume it’ll happen and plan ahead for it. This is the thinking behind having an emergency stash of funds, stored in a safe place.
Some of my favorite hiding places include:
- Secret pocket sewn into your pants
- Behind a patch on your backpack
- Rolled into an empty chapstick container
- Inside a hidden compartment (like this hair-brush or belt pouch)
How much emergency cash? This will be personal preference, but I usually prefer $200 spread out in 2 different places. Some hidden on me, some hidden in my bag. A hidden backup credit card is wise too.
Now if things got really dire, and everything’s gone, what then? You call up a friend or family member, and ask them to send you the emergency money you left with them before you went traveling, via a Western Union or Moneygram transfer.
Hopefully it will never come to that. But these things do happen occasionally, and it’s better to practice safe travel techniques than to remain ignorant about the possibility.
18: Food & Water Safety

After traveling extensively the last 10-years, to over 50 countries, eating all kinds of weird stuff, I’ve only had food poisoning a couple of times.
Don’t be scared of the food when you travel! In fact, eating strange new foods can be a highlight for many people on their adventures around the world.
My food-obsessed friend Jodi recommends the following tips:
- Eat at popular places with long lines
- Try to watch how your food is prepared
- Pack translation cards to express your allergies
- Fully cooked food is always the safest
- Only eat peel-able fruit to avoid bacteria
I also recommend getting a filtered water bottle. In many modern cities around the world the water is safe to drink, but outside of those places it often isn’t.
Sure, you could keep buying bottled water everywhere you go, but that plastic waste is a huge environmental problem. Why not get one sturdy filtered bottle, and re-use it for years?
It pays for itself and saves the environment at the same time!
19: Use ATMs Wisely
You may have been told to cover your hand when keying in your PIN number at an ATM. That’s good advice worth following, both for others looking over your shoulder, as well as hidden cameras trying to record your pin.
Always take a close look at ATM machines before you use them. Pull on the card reader a bit. Does it have any questionable signs of tampering? If so, go into the bank and get someone to come out and check it (and then use another machine, regardless of what happens).
If an ATM machine appears to have eaten your card, run a finger along the card slot to see if you feel anything protruding. The “Lebanese Loop” is a trick where a thin plastic sleeve captures your card (preventing the machine from reading it) – then as soon as you walk away, a thief yanks it out and runs off with your card.
Another overlooked factor is where other people are when you’re at the machine. Can someone peer over your shoulder? Are they close enough they could grab the cash and run off?
If so, use another ATM elsewhere. Better safe than sorry! Never let anyone “help” you with your transaction either.
20: Stop Using Your Back Pocket
It’s the first place any pickpocket will check – and short of putting a loaded mousetrap in there (not recommended if you forget and sit down), the best way to deal with the dangers of having a back pocket is to never use it…
And if putting money in the back pocket of your pants is a habit you can’t seem to break, grab some needle and thread and sew it shut!
Your front pockets are a lot harder to steal from without being noticed.
If you’re REALLY worried, or plan to travel to a city where pickpockets run rampant, you can wear a money belt. I’m not a fan, but I know many who use them for peace of mind.
21: Travel In Numbers

The more people around you, the more eyeballs are on your valuables – and the more legs are available for running after thieves.
A group is also a much more intimidating physical presence, which helps ward off predators of all kinds. It will help to keep you safer than trying to go it alone in a foreign country.
If you’re traveling solo, consider making some new friends and go exploring together.
Staying at backpacker hostels is an excellent way to make some new friends. Often you’ll find other solo travelers there, who may want to do some of the same activities you want to.
However, I’d also like to highlight the importance of not trusting new people TOO quickly. There are some professional scammers who use the backpacker trail to take advantage of other travelers looking for a friend.
Don’t leave your expensive or important stuff with someone you just met. No matter how friendly they seem.
22: Pack A First Aid Kit
Injuries can happen when you travel abroad, not matter how careful you are. That’s why traveling with a basic first aid kit is always a good idea.
You don’t need to go crazy and bring your own needles and scalpels, but stocking the basics to treat cuts, sprains, stomach issues, and burns can help if you or people around you may need them.
I prefer a basic waterproof adventure first aid kit with a few additions of my own:
- Small tube of sunscreen
- Re-hydration salts
- Anti-histamine tablets
- Small pair of scissors
- Extra pain pills (Ibuprofen)
- Emergency space blanket
- Small tube of petroleum jelly (helps prevent blisters)
23: Stay (Relatively) Sober

Getting too drunk or high when you travel is almost always unacceptably risky. If you’re wasted, you’re not present, and anything could be happening around you (or to you).
I’m not saying don’t enjoy yourself. Hell I have plenty over the years! Just do it responsibly, stay hyper-aware of how much you’re consuming, keep hydrated & fed, and make sure you don’t lose control of the situation.
Harder drugs are especially risky — it’s a good way to get in trouble with the police, who may not be as forgiving (or even law-abiding) as authorities back home. Not to mention having to deal with potentially nefarious people who are providing those drugs — and their own alternative motives.
On a similar note, if you’re partial to late nights out partying until pre-dawn hours, be careful assuming that unfamiliar destinations will be as forgiving as back home.
Many generally safe destinations (especially ones filled with tourists) become far less secure late at night – and if you’re stumbling around intoxicated, you’re far less aware of your surroundings – and a VERY easy target for all kinds of bad stuff.
24: Trust Your Instincts!
This one is easily overlooked – and incredibly important.
You are a walking surveillance network. Your body sees and hears more things than you could ever process into coherent thought. Let’s call it your “spidey sense” — the ability to sense danger.
Your body might sense signs of danger before your brain is fully aware.
This is why gut feelings are always worth examining! If you’re feeling uneasy and you don’t know why, try not to write it off as irrational fear. Stop and pay closer attention to the situation. Can you figure out what the problem is?
It’s easy to dismiss your instincts as “silly”. Never treat them as such. Those gut feelings and intuition have kept humans safe for millions of years.
25: Travel Safety For Women vs. Men

All the tips on traveling safely above are equally important for both men and women. I don’t think the ability to travel safely should be focused on gender.
Unfortunately women are victims of violence everywhere, including here in the United States & Canada. Traveling doesn’t necessarily increase that threat, it simply changes the location.
Women worried about being assaulted or harassed might prefer to visit a local street bazaar or nightclub in a group rather than alone. Especially if it’s a common problem for the area.
I know some women who feel safer carrying a safety whistle and door stop alarm when they travel solo too.
However men also have specific safety concerns they need to watch out for, related to their egos. Like getting goaded into a physical fight that isn’t necessary. Or being scammed by a beautiful woman.
Travel safety is really about staying street smart, prepared for the unexpected, and minimizing your exposure to risky situations in a new and unfamiliar country.

A Few Words About Risk…
If you want to travel, you cannot avoid risk. There is no way to be 100% safe from any threat, in any part of life. Risk is an integral part of adventure too.
This means when you hit the road, you’re bound to get scammed sooner or later, or find yourself in unexpectedly challenging circumstances. It happens to all of us.
Risk is unavoidable – but it can be managed, so you can stay safer.
The world is safer than the media sometimes makes it out to be. This isn’t saying that bad things don’t happen. It’s saying they’re usually a misleading representation of what normally happens.
Generally speaking, it’s never been a safer time to travel! So get out there with your new-found knowledge, enjoy your trip with confidence. ★
BOOKING A TRIP SOON?
Here are some travel resources to help you save money & have a great time!
- Ultimate Travel Packing List
- How To Find Cheap Flights
- Tips For Renting A Car Abroad
- How To Save Money Booking Hotels
- Why To Always Get Travel Insurance
- My Best Travel Tips For A Great Trip





